A ransomware attack on UK National Health Service IT services provider, Advanced, has highlighted different attack vectors that cybercriminals are using to target healthcare providers. Advanced provides digital services like patient check-in and NHS 111, both key patient services. Rather than directly target the organisation, attacking a key supplier exposed an alternative weakness that caused major disruption.
In a statement on its website, the Birmingham-based company noted: “On Thursday 4 August 2022, Advanced experienced a disruption to our systems that we have since determined to be the result of a cybersecurity incident caused by ransomware. We immediately took action to mitigate any further risk and isolated all of our Health and Care environments, where the incident was detected. The customer groups impacted either directly or indirectly are Adastra, Caresys, Odyssey, Carenotes, Crosscare, Staffplan and eFinancials.”
While the company took swift action, the attack has still caused significant disruption to the NHS and highlighted the changing threats that healthcare providers are facing.
“This recent attack is yet another example of the evolving adversarial strategy,” reasoned Avishai Avivi, CISO at SafeBreach. “Rather than directly attacking an organisation, in this case, the NHS, they are targeting the organisation’s supply chain. In reading the details available online, my concern is that this attack might have a significantly larger impact than first communicated. It is important to understand that this attack has two distinct impacts: Availability of services impacting operations, and compromise of sensitive Protected/Personal Health Information (PHI).
“Advanced is taking all the correct steps in recovering from the ransomware attack,” continued Avivi. “With that, my concern is that their adjustment recovery time from one week to four weeks indicates an extended ransomware spread, with more systems impacted than originally suspected. While NHS may have taken all the right steps to protect its networks and environments, Advanced was not as rigorous in its efforts.”
“Whenever there is a vulnerability, cybercriminals will seek to exploit it and the NHS and its suppliers are sadly no exception,” added Rob Griffin, CEO at MIRACL. “It’s therefore no surprise that the recent directive from NHS Digital is insisting on deploying multi-factor authentication across its services. Depending on the type of MFA used, this extra layer of protection massively reduces the chances of a credential breach, which remains the main means by which Ransomware is planted. We hope the supplier manages to resolve the situation but this example is another reason why we wholly support this new MFA initiative across the NHS. It really is mission-critical.”
This kind of attack is unfortunately a common scenario, with healthcare seen as a prime target for ransomware attacks. “Healthcare companies and hospitals, in particular, have long been targets of ransomware gangs because they have more money and an urgency to pay,” explained Sam Curry, chief security officer at Cybereason. “That hasn’t gone away in the latest waves, but it has become less visible as new sectors are targeted, including critical infrastructure operators. One could argue that hospitals are part of the critical infrastructure ecosystem already.”
“It’s likely that we will see more attacks of this nature in the coming months,” reflected Jamie Akhtar, CEO and co-founder of CyberSmart. “Classified by the NCSC as a ‘Category One’ attack, this situation does not bode well for the future of UK public sector cybersecurity. Although the NCA states that only a few servers were impacted and disruption was minimal, the consequences of attacks such as these can be devastating.
“In 2020, the world saw the first recorded death as a direct result of a cyberattack,” continued Akhtar. “A German hospital that had suffered a ransomware attack was forced to turn away an ambulance, delaying a patient’s treatment by up to an hour. This delay cost the patient their life. Although this is the first and only recorded incident of a cyberattack directly leading to a loss of life, it’s possible that many more have gone unaccounted for. This story is especially poignant in the wake of the Advanced cyberattack. The Welsh Ambulance Service has admitted that it may take longer for them to respond to calls. In medical emergencies, hours, minutes, or even seconds can mean the difference between life and death – even the slightest disruption caused by cyberattacks can be catastrophic.”
While the consequences for this kind of ransomware attack are now shown to be more than a potential loss of life, the expectation is for attacks on the healthcare sector to become more frequent. “Healthcare has always been a prime target for cybercriminals, but the expanded attack surface of IoT and connected medical devices has exponentially increased vulnerabilities in the last few years,” explained Andy Norton, European Cyber Risk Officer at Armis. “The NHS is particularly vulnerable. Armis’ research of NHS Trusts has shown that ‘suspicious activity’ – including exploit attempts, drive-by attacks, port scans, and connections to the dark web – have risen by 80% since April 2022, though the Trusts’ abilities to protect themselves from these threats have remained the same since pre-April. What is clear from these figures is that NHS infrastructure is being targeted more heavily than ever before, so gaining visibility and understanding of all connected assets is vital to the health of these critical services.”
With data showing healthcare providers facing an increasing risk of ransomware attacks, Cybereason’s Curry has advice for the sector. “My advice for hospitals, and any organisation, is to not pay if you can avoid it. In some cases, you can’t legally pay as with funding terrorism and organised crime, but it’s not a good idea to ever pay unless the cost of doing so affects human life, public safety or is existential. You can’t pay your way out of ransomware, and as Cybereason’s recent global ransomware study proves, companies that admitted paying ransoms were hit a second, third and fourth time by attackers. Sadly, it is often the same criminals doing it. Also, paying doesn’t make the ransomware problem go away since nearly half of the organisations don’t recover data correctly, and it will become public anyway.”
Ransomware attack highlights healthcare supply chain vulnerability

Share this
Related News
The Avenues Riyadh is expected to be the largest…
News
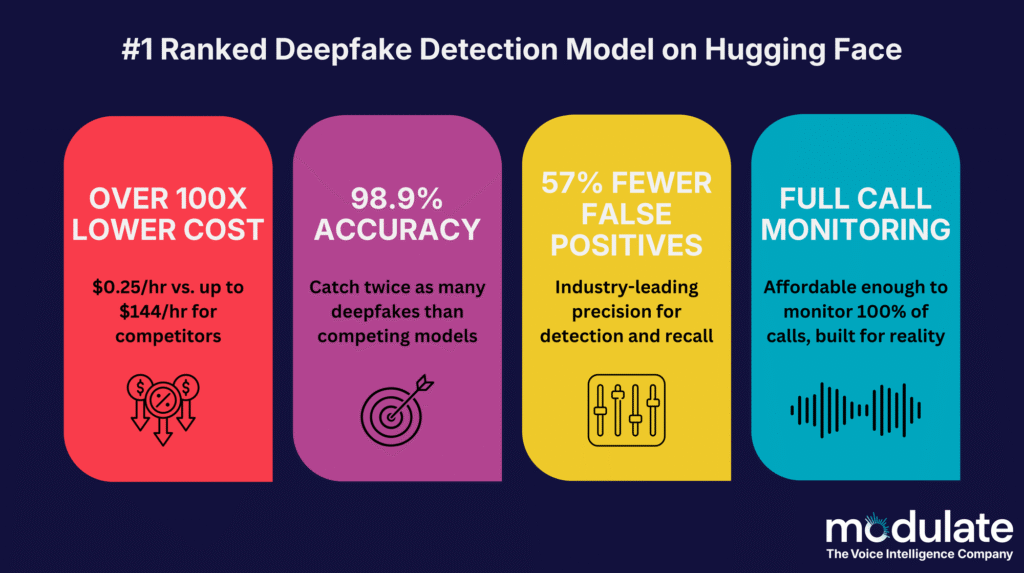
Modulate, the frontier conversational voice intelligence company, has announced…
News
Hirsch Group, a global leader in high-assurance security solutions,…
News