The US Department of Justice has seized 63.7 bitcoins currently valued at approximately $2.3 million which allegedly represent the proceeds of a ransom payment to individuals in a group known as DarkSide. Earlier this year, the group had targeted Colonial Pipeline, resulting in critical infrastructure being taken out of operation.
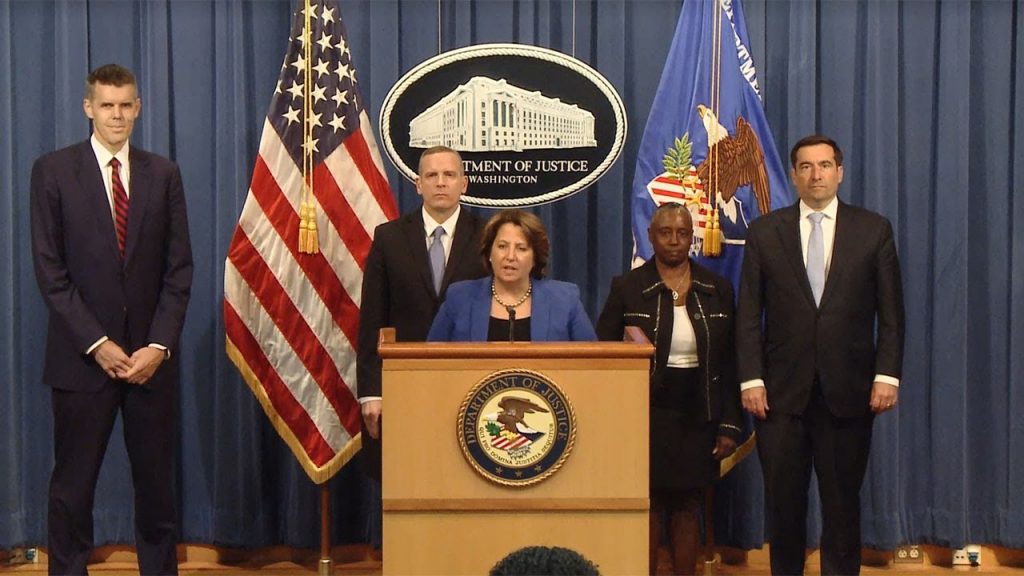
“Following the money remains one of the most basic, yet powerful tools we have,” said Deputy Attorney General Lisa O. Monaco for the US Department of Justice. “Ransom payments are the fuel that propels the digital extortion engine, and this demonstrates that the United States will use all available tools to make these attacks more costly and less profitable for criminal enterprises. We will continue to target the entire ransomware ecosystem to disrupt and deter these attacks. These announcements also demonstrate the value of early notification to law enforcement; we thank Colonial Pipeline for quickly notifying the FBI when they learned that they were targeted by DarkSide.”
“There is no place beyond the reach of the FBI to conceal illicit funds that will prevent us from imposing risk and consequences upon malicious cyber actors,” added FBI Deputy Director Paul Abbate. “We will continue to use all of our available resources and leverage our domestic and international partnerships to disrupt ransomware attacks and protect our private sector partners and the American public.”
“Cyber criminals are employing ever more elaborate schemes to convert technology into tools of digital extortion,” noted Acting US Attorney for the Northern District of California Stephanie Hinds. “We need to continue improving the cyber resiliency of our critical infrastructure across the nation. We will also continue developing advanced methods to improve our ability to track and recover digital ransom payments.”
Colonial Pipeline was the victim of a ransomware attack resulting in the company taking portions of its infrastructure out of operation. Colonial Pipeline reported to the FBI that its computer network was accessed by an organisation named DarkSide and that it had received and paid a ransom demand for approximately 75 bitcoins.
As alleged in the supporting affidavit, by reviewing the Bitcoin public ledger, law enforcement was able to track multiple transfers of bitcoin and identify that approximately 63.7 bitcoins, representing the proceeds of the victim’s ransom payment, had been transferred to a specific address, for which the FBI has the “private key,” or the rough equivalent of a password needed to access assets accessible from the specific Bitcoin address. This bitcoin represents proceeds traceable to a computer intrusion and property involved in money laundering and may be seized pursuant to criminal and civil forfeiture statutes.
The Special Prosecutions Section and Asset Forfeiture Unit of the US Attorney’s Office for the Northern District of California is handling the seizure, with significant assistance from the Department of Justice Criminal Division’s Money Laundering and Asset Recovery Section and Computer Crime and Intellectual Property Section, and the National Security Division’s Counterintelligence and Export Control Section. The Department components who worked on this seizure coordinated their efforts through the Department’s Ransomware and Digital Extortion Task Force, which was created to combat the growing number of ransomware and digital extortion attacks.
Commenting on the recovery of the funds Chris Grove, product evangelist at Nozomi Networks stated: “The joint action and collaboration by the government and National Cyber Investigative Joint Task Force is exactly what defenders are asking for. Defending against run-of-the-mill threats is affordable, and achievable. Some threats rise to a new level, and must be dealt with differently. While it’s great that the government recovered some of the $4.4 million paid by Colonial Pipeline, we can’t lose sight of the fact that while Colonial is a happier ending story, there are dozens of victims we can also discuss who haven’t fared as well. Not to mention 100s we know about, but can’t discuss, and another 1,000 that we don’t even know about. We need to keep our eye on the ball and continue to build our defences, while using actions like those today, as a way to trim the weeds that grow too tall.”
“There is no doubt an incredible story behind the scenes that we look forward to hearing more about,” added Sam Curry, chief security officer at Cybereason. “These developments have put threat actors on notice, and for the ransomware writers and other malware authors – now the gloves are off. However, this sends a clear message to the criminals: you are not immune to repercussions. Ransomware gangs are, in a dark sense, startups with their own venture capital and business models. The ‘investors’ in these organisations must be getting nervous that their ill-gotten gains can be recouped.
“Now is the time for law enforcement agencies and other important players in the public and private sector to continue in the same vein and put pressure on all fronts: technological, economic and diplomatic,” continued Curry. “It is far past time to let the malware authors and the cyber criminal gangs know that they have been put on notice and that their criminal enterprises will be exposed one by one. Now, it is hoped that the recovery of more than $2 million leads to Russia distancing itself in a face-saving way and moving ransomware gangs and cybercriminal outfits clearly into the pirate category. In other words, truly make it clear that they are enemies of the connected world.”