It has been reported that Anthropic has launched Project Glasswing, an initiative where AI is used to identify and remediate undiscovered vulnerabilities in critical software. Here, experts at Talion, Closed Door Security and CybaVerse respond to the news.
Liam Salsi, Director of Architecture at Talion, commented: “Projects like Glasswing highlight just how far large language models have evolved, to the point where their potential for both defensive and offensive cyber use is now being tightly controlled. The decision to restrict access to a small group of trusted partners reflects not just the power of these systems, but the risks associated with wider release.
“These closed collaborations are not only about identifying and remediating vulnerabilities in a controlled way, they are also critical in shaping the guardrails and refusal mechanisms needed to safely operationalise this capability at scale.
“The challenge is that models developed at this level by major AI providers will not remain exclusive for long. Actors with similar resources, including nation states and well-funded criminal groups, are likely already developing or replicating comparable capabilities.
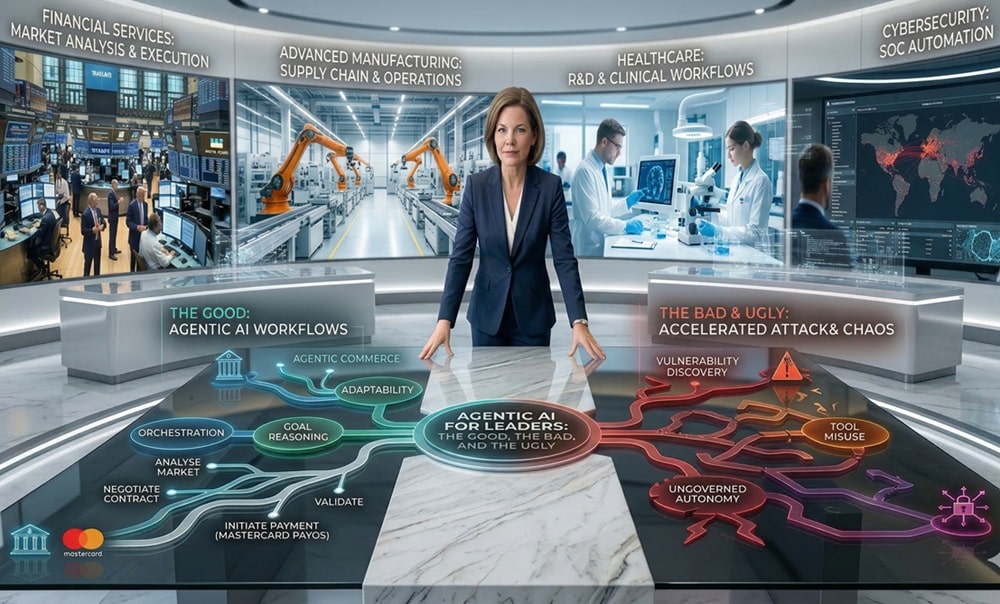
“This is a clear signal of the cyber arms race now underway, where AI is being used both to uncover vulnerabilities and to defend against their exploitation. It also marks a shift beyond the use of AI as a support tool in secure code review, towards AI playing a far more active role in identifying weaknesses across complex environments.
“It’s also important to note that this does not render existing security controls obsolete. Many of the vulnerabilities identified through programmes like Glasswing would still be detectable and preventable through layered security approaches and mature SOC capabilities.
“However, what changes is the scale.
“AI will increase the speed and volume at which vulnerabilities are discovered and potentially exploited, placing greater pressure on organisations to respond at pace. The ability to scale detection and response will become a defining factor in how effectively organisations can manage this next phase of cyber risk.”
William Wright, CEO, Closed Door Security, said: “The most worrying aspect of Mythos isn’t its bug detecting capabilities; it’s the potential autonomy.
“Many stories about AI detection of novel exploits in bugs in recent years have in some ways been unremarkable. LLMs have already been used to detect numerous potential exploits and vulnerabilities, but this isn’t strictly because the models are always powerful. More often than not, it’s because there were no humans looking at the same problem. If current models were as impactful as some claims make them out to be, then SAST would have ceased to exist. Models are highlighting things in codebases that current SDLCs are not securing properly, representing less the existential capabilities of AI models and more the failure in general approaches to software development.
“The real impact of LLMs so far has been in speed and scale, and they’re being used to automate code review on an industrial level.
“However, even automated code review still requires manual human verification, both to ensure detected vulnerabilities are valid, and verify that AI-generated patches don’t introduce further holes.
“Mythos’ reported capabilities over older models could mean an entirely new shift, away from slower review and verification, to fully automated scanning and exploitation of vulnerabilities. Responsible developers won’t stop manual verification, but for threat actors this could be a huge step up in capability.
“Attackers could work around the clock, pointing models at all parts of an organisation’s tech stack, probing for potential exploits in every corner. Larger organisations integrate huge amounts of disparate third-party software into their core operations, much of it obscure, and understanding and combating this risk is already a huge undertaking.
“We’re rapidly approaching a world where attackers would no longer need state-level backing to discover and exploit devastating zero-days, and even petty cybercriminals could inflict devastating damage using novel exploits.
“We can only hope that LLMs’ defensive capabilities are enough to counterbalance this, and that organisations start to prioritise response and vigilance moving forward.”
James Disley, Senior SOC and IR Analyst, CybaVerse, said: “Anthropic says Mythos has already found thousands of high-severity vulnerabilities, including in every major operating system and web browser.
“Anthropic also says it is making the model available to Project Glasswing partners and to more than 40 additional organisations that build or maintain critical software infrastructure, rather than releasing it publicly.
“Keeping the model private may reduce the risk of immediate widespread misuse, but it also limits outside scrutiny and makes independent verification of Anthropic’s claims difficult.”
Read more about Project Glasswing, here
For more cybersecurity news, click here