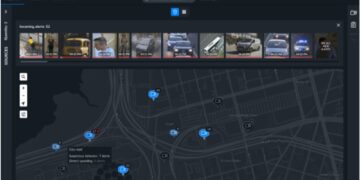
It has been reported by Bloomberg that video surveillance manufacturer Verkada is the latest high-profile company to be the victim of hackers. Details of the hack and the companies affected have been widely covered in various reports, but what does this attack mean for the wider surveillance industry? And how should other manufacturers protect themselves from suffering the same fate? We asked a panel of industry experts for their opinions.
“The reports of the hacktivist breach of more than 150,000 surveillance cameras used inside Tesla’s warehouses, police stations, jails and hospitals around the world, is a reminder that even though recent nation-state cyber attacks on SolarWinds and Microsoft Exchange Servers are garnering headlines, hacktivist groups are still players in the global cyber ecosystem,” said Sam Curry, chief security officer at Cybereason. “This breach appears to have been preventable if the administrator’s username and password weren’t exposed on the internet. Preventative medicine starts when user credentials are frequently updated and security awareness training is regularly offered. Today, there are more than 1 billion surveillance cameras in use around the world and security is an afterthought in many of them, resulting in spying and unlawful monitoring of unsuspecting victims.”
“The successful compromise of IoT devices such as surveillance cameras, is rapidly becoming a consistent occurrence,” noted Natalie Page, Threat Intelligence Analyst, Talion. “IoT devices are highly vulnerable to intrusions, due to their inability to perform regular software security updates as a computer does, something which adversaries understand all too well. This attack against such a high-profile organisation, permitting attackers access to highly intrusive surveillance cameras is extremely disturbing. Our modern world relies heavily on surveillance, built on billions of cameras which observe our every move. We have essentially created an infrastructure which all adversary classifications across the threat landscape can leverage to achieve their goals.”
“IoT security cameras are extensively used by industry and the critical infrastructure sector,” added Andrea Carcano, co-founder at Nozomi Networks. “Given their prevalence and growing use, it’s important to understand the security risks of IoT cameras. We urge you to take measures to prevent unauthorised access to audio/video streams and CCTV user credentials.”
“Every computer system in the cloud has one major weakness, the password to access the accounts that matter most,” reflected Patrick Hunter, EMEA Director at One Identity. “What did Verkada do wrong? Well, they allegedly didn’t have control over the one account that they needed to. It is possible that the account wasn’t monitored and that the password wasn’t regularly changed on a rotation basis. But the biggest error was underestimating the power of one single account to undo their business and grant access to everyone’s data. At the very least, there should have been some form of multifactor authentication to protect the account. Whenever anyone accessed it, they would have to prove that they were who they said they were. Simple, cheap and effective as a first line of defence.”
“Privacy and industry regulators will be examining Verkada operations to assess whether appropriate controls were in place to protect these highly sensitive and regulated data types,” observed Niamh Muldoon, Global Data Protection Officer at OneLogin. “While the root cause analysis has not been shared, it’s fair to say that access controls to physical security systems and components often gets forgotten about or tends to be exempt due to the complexities of outsourcing, being on a separate network and the technical integration limitation. Leaders in the IAM space have addressed these complexities and provide trusted platforms that can streamline access, enforce strong authentication mechanisms with the ability to monitor, report and alert – reducing risk of unauthorised access.”
“This attack highlights how the internet of things is expanding the attack surface and providing new avenues for cybercriminals to target organisations,” said Stephen Kapp, CTO and Founder of Cortex Insight. “The attack also reinforces the importance of organisations applying security controls around all devices connected to the network as this will limit the chances of intruders gaining remote access to them for nefarious purposes. This sort of device should never be directly connected to the internet.”